The impact of Big Data of International Affairs
Big Data is changing our lives, but does it also change international politics? Andrej Zwitter, active at the University of Groningen as professor by special appointment of NGIZ, argues that Big Data is influencing international politics on ways we only recently started to notice. To measure the impact Zwitter explores new possibilities and risks in the areas of humanitarian aid, development and international security.
On November 26, 2008, ten heavily armed men of the Lashkar-e-Taiba (LeT) attacked Mumbai in what became one of the worst cases of terrorism supported by public and social media informed intelligence. With a press of a button the Pakistan-based operations center, which kept in touch with the armed attackers via GSM and satellite phones, were able to identify the most important targets, the status of the Indian government’s response, and even personal profiles of hostages they kept in the Taj Mahal Palace hotel, based on openly accessible information gathered from the internet (open source intelligence, OSINT).
In one instance, a bystander tweeted a photo of police officers advancing onto the besieged Jewish community building, which was promptly intercepted by the operations center and used to alert the attackers, which used this information to ambush the police officers.[1]
Big Data is the key
This is just one of many examples illustrating the threats that have accompanied the positive sides of modern technology and the omnipresence of the internet. The key concept for understanding this and other similar scenarios is Big Data. While many have heard about the term, only a few have a concrete idea what Big Data actually entails and even fewer have thought about the implications of Big Data regarding international affairs. This article develops the idea that Big Data increasingly affects politics in manifold ways. In part, international politics have already experienced such change with the ascend of cyber space as important domain of daily activity. With Big Data this change is not only accelerating, but it unveils new dimensions, which we, as political scientists and observers of international affairs, are only now learning to comprehend.
As political scientists and observers of international affairs we are only now learning to comprehend
What is Big Data?
The novelty of Big Data requires us to take a look at its definitions. Apart from being big amounts of data there are more features relevant to the understanding of this relatively young phenomenon. Looking at different definitions and descriptions one can distill its most important features.
The classics are the three Vs:
· Volume: consisting of massive amounts (measured today in petabytes [1015 bytes], exabytes [1018 bytes] and zetabytes [1021 bytes] and soon to be measured in yottabytes [1024] = 250 trillion Dvds); according to Smolan and Erwitt, from the beginning of History till 2011 5 billion gigabytes were produced – in 2015 this amount is produced every 10 seconds.[2]
· Velocity: the speed of data creation and its collection approaches real-time.[3] This not only concerns questions of bandwidth but also of implementing IT architectural solutions that can cope with the data (e.g. Hadoop, an open-source software for distributed computing of massive data sets).[4]
· Variety: encompassing structured and unstructured data, different formats and units of analysis, such as documents, emails, social media messages, YouTube videos, pictures, audio, radio-frequency identification (RFID) tags, satellite imagery, sky cartography, DNA sequencing, phone network call data, cell phone GPS signals etc. Furthermore, it includes data from different sources, self-generated, data scraped from the web, or retrieved from other outside sources.[5]
Big Data, with all its problems and shortcomings, promises an information advantage, be it in business intelligence, state intelligence or any other form of data gathering and analysis. The promises are to become, if not omnipotent, at least omniscient – a promise no business or government is not at least tempted by and one that criminals are readily tapping into.
At the same time, new forms of data analytics (particularly those that build on machine generated algorithms and replace causation with correlation) raised questions about whether we are encountering a new epistemic era of radical empiricism in which theories will have been a thing of the past.[6]
Big Data and International Relations Theory
With Big Data, most certainly, the human being as individual actor in world affairs, has shifted into the focus of research and theorization. Thinking about individual agency in ethics as well as in international relations theory builds on at least three elements of attribution:[7]
1. Causality: If the result is causally connected to an agent’s action, then one can attribute this act to the actor.
2. Knowledge: If an agent has knowledge of the consequences of its actions, intentionality can be attributed.
3. Choice: If the agent had no choice to act differently without more harm for itself or for others, no grounds of justification or excuse can be brought forth.
This form of agency attribution associated with individuals implies individual causality. In much of the international relations (IR) literature, individual relevance for causal attribution has been downplayed (because of the quite evident need to simplify theory and reduce actors for the sake of simplifying the analysis of reality).
For example, realism considers non-state actors as mere proxies to states when it comes to international affairs; and liberalism might accept the host of corporate actors inhabiting the cyber domain (also called the fifth domain of warfare), but has a difficulty handling individual actors and single-issue groups of opportunity like Anonymous.
However, the role of social media in the Arab Spring,[8] Snowden’s leaking of NSA files, or the use of Facebook, Twitter and YouTube by terror organizations,[9] raises the question about whether the role of Big Data might require a rethinking of the individual’s role in IR.

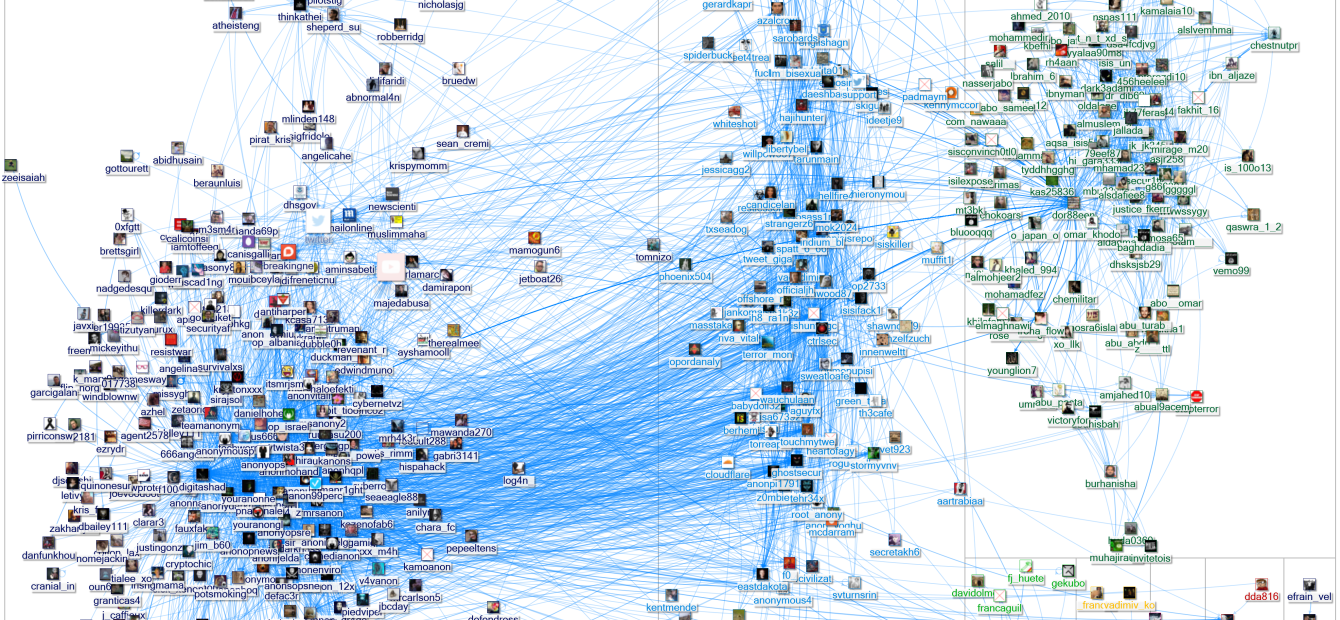
Anonymous against ISIS
The interaction between individuals, for example hacker conglomerates such as Anonymous and LulzSec or even more loosely associated single purpose groups that helped spread word about the Arab Uprisings through Facebook and Twitter, illustrate a changing power relationship in international affairs. Increasingly we find that states’ powers in the fifth domain of cyber are matched by operating capabilities of loosely affiliated groups operating in an inherently decentralized way.
One example is the declaration of war by the hacker group Anonymous against ISIS by in the beginning of 2015. Operation ISIS (#OpISIS) targets mostly the online presence (websites, Facebook and Twitter accounts) of ISIS affiliates. At one instance the media reported that hackers associated with the Anonymous group had taken down several thousand ISIS related Twitter accounts. This happened not necessarily to the appreciation of state intelligence agencies, which got most of their intelligence about ISIS from information gathered from these sources.[10]
While the individual alone might still be relatively powerless, these small ad hoc groups give us already an entirely different view on distributed agency, i.e. an agency that is for its capability of morally relevant action dependent on other actors (if only a few). One could call this agency, which is for its capability to act dependent on other actors, a dependent agency. Floridi refers to these moral enablers, which hinder or facilitate moral action, as infraethics.[11]
Big Data has induced a hyper-networked world society, in which it is easier than ever before to engage in common political causes irrespective of national boundaries
The network nature of society, however, means that this dependent agency is always a factor when judging the moral responsibility of the agent. Big Data has induced a hyper-networked world society, in which it is easier than ever before to engage in common political causes irrespective of national boundaries. This changes foundational assumptions about ethical responsibility in international relations theory by changing the nature of power of actors in the fifth domain: namely an inherent shift towards informational/soft power.
This changing set of actors is, as also below examples of crisis mappers etc. illustrate, tied into the shifting nature of power from the physical to the informational.
Big Data for Peace and Justice
The ethical dimension becomes particularly evident when taking a closer look at the use of Big Data in the areas of peace, security and aid. Humanitarian and development aid are dependent on reliable data for operational planning, logistics and monitoring of their projects. In order to facilitate this, several platforms have been developed to provide humanitarian aid workers with open access to information (and many more are mushrooming every year).
This sharing of data is a prerequisite to facilitate aid delivered by NGOs that otherwise do not have readily access to the latest information or have the capability of gathering intelligence on the ground themselves.
For example, when disaster strikes humanitarian operational planning based on a rapid needs assessment (RNA) should usually be ready 72 hours after the beginning of the disaster. In this regard, quite a few innovations have tried improving the information gap that many organizations have been facing.
Crisis mappers
Ushahidi was developed as a platform that offered the ability to upload information about crises from a GPS enabled cellphone in real-time onto a map accessible for everyone.[12] It was extensively used to support humanitarian operations after the Haiti earthquake in 2010, but also served to improve the election monitoring in Kenya 2013 (Uchaguzi project), among many other examples.[13]
Similarly, the Standby Task Force, Sahanna and other crisis mappers use overlay technology to project crowd-sourced information provided often by volunteers onto maps to inform humanitarian and development aid workers.
The Digital Humanitarian Network (DHN), an umbrella group of 16 volunteer technology organizations brings together expertise in geographical information systems, online mapping, data analysis and statistics in order to develop user-friendly tools for volunteers to contribute to relief efforts through the crowd-sourced mapping of man-made and natural disasters.[14]
Humanitarian Data Exchange (HDX) is a project launched by OCHA containing more than 1500 datasets ranging from databases aggregating the number of Ebola cases and infected aid workers, water sources and opinions about water quality in Kenya, to a database of total uniformed personnel contributions of each contributing country by month, by type (troop, police, or expert/observer) and by mission.
Data for Development Challenge
Furthermore, in 2012 the global telecommunications company Orange launched its first and in 2014 its second "Data for Development Challenge" (D4D). For the purpose of the challenge, in which academic and development organizations compete over the best applications for mobile data, Orange provides the teams with datasets containing:[15]
- communications between antenna tower;
- a sample of movement routes: location by mast;
- a sample of movement routes: location by administrative unit;
- a synthetic data set; and
- weather data.
Participants in the first D4D challenge showed for example that human movement is surprisingly predictable and useful for forecasting the spread of diseases. Another project used the telecommunications data to provide insights about the geography of social ties and social divisions.[16]
Potential for misuse
While these developments promise great insights into the nature of epidemics, help improve the delivery of aid and strengthen the resilience of local communities against sudden onset and protracted crises, Big Data in this area bears a huge potential for misuse.
It suffices looking at the amount of aid works that become victims of armed attacks. In 2013 alone, there were 251 separate attacks against civilian aid operations, affecting 460 aid workers. Of these, 155 aid workers were killed, 171 were seriously wounded, and 134 were kidnapped.[17]
Aid workers, particularly since the shift from in-kind to cash-based aid, are travelling with much money, hardly any security (many aid organizations consider military escorts a violation of the humanitarian principles) and with expensive equipment (such as Toyota Land Cruisers, the standard vehicle of humanitarian aid workers).
If humanitarian actors have access to these crowd-sourced tools for their operational planning, so do criminals and armed actors ready to profit from the caravans of goods ready for the taking. Furthermore, location tracking of internally displaced persons (IDPs) might be just as useful for humanitarian aid workers as it is for the armed factions from which the IDPs are trying to escape.
Open Data
The potential for misuse and the criminal innovation that Big Data in the area of development and humanitarian aid might experience is limited only by the imagination of malevolent actors. The biggest risk, here stems from what is termed Open Data, i.e. databases and open source information accessible to everyone.[18]
Examples of misuse of open crowd-sourced data are manifold, as Raymond, Howarth and Hutson describe, such as the Taliban attacks on Word Food Program distribution points and clinics of Médecins Sans Frontières responding to the 2010 Pakistan floods and food crisis, facilitated by location data provided by crisis mappers.[19]
Data might in the near future indeed not only be a source for the improvement of aid, but the very thing that will also lead to the a digital humanitarian crisis
Open Data, consisting of new media (text, photo, and video content generated by individuals through social media applications), crisis mapping based on crowd-sourcing, and other forms of Big Data (e.g. the internet of things, IoT), might in the near future indeed not only be a source for the improvement of aid, but the very thing that will also lead to the a digital humanitarian crisis.
National and international security
With regards to national and international security, Big Data also already plays an important role. On the domestic and international level the massive use social media has become common practice. For example 95% of the police forces are actively using social media for reaching out to the public, for investigative and intelligence gathering purposes etc.[20]
One of the recent advance of Big Data happened in the area of predictive policing for forecasting crime hotspots to spatiotemporal analyses to risk terrain analyses.[21] Also the US military has accepted cyber as another (the fifth) domain of war, after land, sea, air and space.[22]
Automated bots
This domain of warfare has very readily been occupied by state and non-state actors and the forms of warfare include Distributed Denial of Server Attacks (DDoS) for taking down websites and servers, viruses for targeting of critical infrastructure (e.g. StuxNet), attacks on individual’s online presence (e.g. identity theft), massive online campaigning, manipulation of mass audiences (social engineering), and recruiting of terrorists through social media.
Thereby the agents are by no means solely human. A 2013 report conducting a detailed analysis of web-traffic found that a staggering 61,5% of website visitors were automated bots (with an increasing tendency), half of which consists of “good bots”, necessary for search engines and other services, the other half of malicious bot types such as scrapers (5%), hacking tools (4,5%), spammers (0.5%) and with an amount of 20,5% impersonators for the purpose of market and state intelligence and manipulation.[23]
Twitter bombs
The following two examples might serve to illustrate the capability and the actual cyberwar operations that are currently going on. Early 2015, the Intercept released leaked information that the British intelligence agency GCHQ had launched “Operation QUITO” in 2009, an operation design to use social media and other tools in the cyber domain to ensure the continuation of Britain’s rule over the Falklands.
At the heart of the operation was the Joint Threat Research and Intelligence Group (JTRIG), whose task was to develop surveillance (online Human Intelligence – HUMINT) and effects operations “preventing Argentina from taking over the Falkland Islands by conducting online HUMINT”.[24] JTRIG would be using tools and techniques that would allow mass delivery of emails and SMS as well as audio messages to telephones, the masquerading of Facebook pages for individuals and even whole countries, to artificially increase traffic to a website or its page views, to change the outcomes of online polls, and inflate the view count on media websites such as Youtube, to name but a few tools.[25]
A similar strategy was used back in 2010 when hackers planted so called Twitter-bombs to manipulate the election over the senate seat of Ted Kennedy in favor of the republican candidate. The Twitter-bomb – the practice is called Astroturfing – created fake Twitter accounts that would automatically post derogatory messages about the democratic candidate, thereby creating the appearance of a legitimate grassroots debate.[26]
The UN Secretary General detailed in a report how the use of technology has shifted from being a mere utility to becoming an intrinsic part of decision-making
There are, however, also positive aspects relating to peace and security concerning Big Data. Also the United Nations, next to NGOs, is increasingly getting involved in the use of data for improving humanitarian action, as has been shown already above.
In October 2014, the UN Secretary General detailed in a report to the General Assembly how the use of technology (Big Data, social media and other tools) has shifted from being a mere utility to becoming an intrinsic part of decision-making, information gathering and a planning tool in support of the United Nations’ core mandates in the areas of peace and security, development, human rights and international law.
“Networks of organizations and individual volunteers use online platforms for collaborative data gathering, processing and publishing to help support relief efforts. Various technologies and methods range from relatively simple data gathering, to highly sophisticated sensor technology and analytics. The increasing availability of free and open-source software and open data reinforce the need for the United Nations to collaborate in the movement of big data, joined with humanitarian and social networking.”[27]
For that purpose, he laid out a strategy to strengthen, and provide a common vision for, the delivery of information and communications technology in the United Nations focusing on improving the internal ICT capabilities and increasingly investing in Big Data innovations.[28]
Peacekeeping and peacebuilding
Researchers already envision the role that Big Data can play for the purpose of peacekeeping and peacebuilding.[29] John Karlsrud in his very insightful chapter, for example, argues that the already ongoing cyberization of conflict prevention, humanitarian action and development with initiatives such as Ushahidi, Syria Tracker, the possibility of tracking population flows regarding internal displacement, etc. should finally lead to a new generation of peacekeeping (peacekeeping 4.0) and peacebuilding that embraces the advancements in real-time awareness, feedback and early warning that Big Data has to offer.
After all “[b]eing able to access, analyze, and use big data should be imperative for peacekeeping and peacebuilding operations, which by definition find themselves operating in volatile situations.”[30]
International justice
Also in the area of international justice Big Data has become an important source of information. Satellite imagery is increasingly becoming another source Big Data analytics. Location data correlated with surveys, photos and maps can answer a variety of questions in the area of financial services, retail, policing, and even international justice as in the uncovering of war crimes.[31]
For example, in 2011, the Satellite Sentinel Programme of the Harvard Humanitarian Initiative reported to have found eight mass graves in and around Kadugli (Sudan) with the help of analyzed DigitalGlobe imagery corroborated with details retrieved from UN reports and eyewitness accounts.[32]
Prediction and forecasting
Big Data also comes into play concerning the prediction and forecasting of conflicts and social instabilities. For example, the US Defense Department’s Information Volume and Velocity program aims to harness strategic intelligence from Big Data by use pattern recognition to detect social instabilities in populations that would point to emerging conflicts.[33]
The UN initiated the Global Pulse, a Big Data based project to track real-time developments regarding human wellbeing and growing vulnerabilities. “The initiative was established based on a recognition that digital data offers the opportunity to gain a better understanding of changes in human well-being, and to get real-time feedback on how well policy responses are working.”[34]
This has led some commentators to cautiously hoping that Big Data might in future be able to prevent conflicts before they happen.[35]
Conclusion
Kremer and Müller have argued that “the global cyberspace substrate has undermined the older distinctions between international and domestic, between peace and war, between state and non-state actors, and between technology, politics, and economics.”[36]
One probably has to develop their conclusions even further to argue that the fifth domain threatens to radically reshape our understanding of international relations and ethics. This will consequently have to lead to a rethinking and reformulating of theories of international relations, ethical attribution, and just war theory.
Among the many challenges that arise with Big Data, governance efforts should strive to reduce that sensitive information (among many more issues for example the location of humanitarian actors and IDPs) does not become Open Data, which is accessible to and exploitable by malevolent actors.
Global awareness
Most importantly, however, one task is left to states, international organizations and the civil society. In order to reduce the vulnerabilities that Big Data has imposed on society, knowledgeable stakeholders need to raise the awareness of people about the intricacies that Big Data and their digital footprint bring with them.
Big Data certainly holds the promise for improving global well-being and even preventing conflicts. Nevertheless, it can also be the source of much evil. The only way to keep the misuse of Big Data in check is to create a global awareness and to use the tools Big Data itself offers, social media and global connectedness, to enable society to become the public watchdog of the Big Data age.
Prof. Dr. Andrej Zwitter is NGIZ Chair for International Relations at the Department of Legal Theory, University of Groningen, The Netherlands, and honorary senior research fellow at Liverpool Hope University as well as senior research fellow at the Austrian Institute for International Affairs (oiip). This article was produced as part of the cooperation between the Austrian Institute for International Affairs and the Danube University Krems, Austria.
[1] Marc Goodman, Future Crimes: Everything Is Connected, Everyone Is Vulnerable and What We Can Do About It, ebook (New York: Knopf Doubleday Publishing Group, 2015), chap. 6.
[2] Rick Smolan and Jennifer Erwitt, The Human Face of Big Data (Sausalito, Calif.: Against All Odds Productions, 2012).
[3] Rob Kitchin, “Big Data and Human Geography Opportunities, Challenges and Risks,” Dialogues in Human Geography 3, no. 3 (November 1, 2013): 262–67, doi:10.1177/2043820613513388.
[4] Doug Laney, 3D Data Management: Controlling Data Volume, Velocity, and Variety (Meta Group, February 6, 2001), http://blogs.gartner.com/doug-laney/files/2012/01/ad949-3D-Data-Management-Controlling-Data-Volume-Velocity-and-Variety.pdf.
[5] Bill Vorhies, “How Many ‘V’s in Big Data – The Characteristics That Define Big Data,” Business Foundation Series, #2, October 31, 2013, http://data-magnum.com/how-many-vs-in-big-data-the-characteristics-that-define-big-data/.
[6] Rob Kitchin, “Big Data, New Epistemologies and Paradigm Shifts,” Big Data & Society 1, no. 1 (April 1, 2014): 2053951714528481, doi:10.1177/2053951714528481.
[7] Merel Noorman, “Computing and Moral Responsibility,” in The Stanford Encyclopedia of Philosophy, ed. Edward N. Zalta, Fall 2012, 2012, http://plato.stanford.edu/archives/fall2012/entries/computing-responsibility/; Andrej Zwitter, “Big Data Ethics,” Big Data & Society 1, no. 2 (July 1, 2014): 2053951714559253, doi:10.1177/2053951714559253.
[8] Regarding the role of social media during and the Arab Spring compare: Gadi Wolfsfeld, Elad Segev, and Tamir Sheafer, “Social Media and the Arab Spring Politics Comes First,” The International Journal of Press/Politics 18, no. 2 (April 1, 2013): 115–37, doi:10.1177/1940161212471716; Habibul Haque Khondker, “Role of the New Media in the Arab Spring,” Globalizations 8, no. 5 (October 1, 2011): 675–79, doi:10.1080/14747731.2011.621287.
[9] Gabriel Weimann, “Terror on Facebook, Twitter, and Youtube,” Brown Journal of World Affairs 16, no. 2 (2010): 45–54.
[10] Jasper Hamill, “Why Are Spooks ‘Furious’ with Anonymous Drive to Name and Shame ISIS Members?,” News, Mirror, (March 18, 2015), http://www.mirror.co.uk/news/technology-science/technology/spooks-left-furious-after-anonymous-5355738.
[11] Luciano Floridi, “Distributed Morality in an Information Society,” Science and Engineering Ethics 19, no. 3 (2013): 727–43.
[12] “Ushahidi,” accessed April 16, 2015, http://www.ushahidi.com/.
[13] “Uchaguzi - Kenyan Elections 2013 - Community Wiki - Ushahidi,” accessed April 16, 2015, https://wiki.ushahidi.com/display/WIKI/Uchaguzi+-+Kenyan+Elections+2013.
[14] Declan Butler, “Crowdsourcing Goes Mainstream in Typhoon Response,” Nature, November 20, 2013, doi:10.1038/nature.2013.14186.
[15] “The Second ‘Data for Development’ (D4D) Challenge in Africa | United Nations Global Pulse,” accessed April 16, 2015, http://www.unglobalpulse.org/D4D-Challenge-Senegal.
[16] Jennifer Poole, “Winning Research from the Data 4 Development Challenge | United Nations Global Pulse,” Global Pulse, (May 6, 2013), http://unglobalpulse.org/D4D-Winning-Research.
[17] Aid Worker Security Report 2014 - Unsafe Passage: Road Attacks and Their Impact on Humanitarian Operations, Aid Worker Security Database (AWSD) (Humanitarian Outcomes, 2014), https://aidworkersecurity.org.
[18] UN Secretary General, Information and Communications Technology in the United Nations, Report of the Secretary General pursuant to A/Res/67/254 (New York, October 10, 2014), http://www.un.org/en/ga/search/view_doc.asp?symbol=A%2F69%2F517.
[19] Nathaniel Raymond, Caitlin Howarth, and Jonathan Hutson, “Crisis Mapping Needs an Ethical Compass,” Gobal Brief, February 6, 2012, http://globalbrief.ca/blog/2012/02/06/crisis-mapping-needs-an-ethical-compass/.
[20] Center for Social Media, 2014 Social Media Survey Results, Annual Survey (Alexandria, VA: International Association of Chiefs of Police, Fall 2014), http://www.iacpsocialmedia.org/Resources/Publications/2014SurveyResults.aspx.
[21] Walter L. Perry et al., Predictive Policing: The Role of Crime Forecasting in Law Enforcement Operations (Santa Monica, CA: RAND Corporation, 2013), http://www.jstor.org/stable/10.7249/j.ctt4cgdcz.
[22] “War in the Fifth Domain,” The Economist, July 1, 2010, http://www.economist.com/node/16478792.
[23] Igal Zeifman, Bot Traffic Is up to 61.5% of All Website Traffic, 2013 Report (Incapsula.com, December 9, 2013), http://www.incapsula.com/blog/bot-traffic-report-2013.html.
[24] Andrew Fishman and Glenn Greenwald, “Britain Used Spy Team to Shape Latin American Public Opinion on Falklands,” The Intercept, April 2, 2015, https://firstlook.org/theintercept/2015/04/02/gchq-argentina-falklands/.
[25] “JTRIG Tools and Techniques,” The Intercept, July 14, 2014, https://firstlook.org/theintercept/document/2014/07/14/jtrig-tools-techniques/.
[26] Rachel Ehrenberg, “Social Media Sway: Worries Over Political Misinformation on Twitter Attract Scientists’ Attention,” Science News 182, no. 8 (October 20, 2012): 22–25.
[27] UN Secretary General, Information and Communications Technology in the United Nations, para. 40.
[28] UN Secretary General, Information and Communications Technology in the United Nations.
[29] Sanjana Hattotuwa, “Big Data and Peacebuilding,” Stability: International Journal of Security & Development 2, no. 3 (November 19, 2013): 59, doi:10.5334/sta.ct.
[30] John Karlsrud, “Peacekeeping 4.0: Harnessing the Potential of Big Data, Social Media, and Cyber Technologies,” in Cyberspace and International Relations: Theory, Prospects and Challenges, ed. Jan-Frederik Kremer and Benedikt Müller, 2014 edition (New York: Springer, 2013), 155.
[31] Natasha Léger, “Satellite Imagery Is the Ultimate Big Data,” LBx Journal, December 11, 2014, http://www.lbxjournal.com/articles/satellite-imagery-ultimate-big-data/260516.
[32] Satellite Sentinel Project, Evidence of Burial of Human Remains in Kadugli, South Kordofan, Special Report (Harvard Humanitarian Initiative, August 24, 2011), http://hhi.harvard.edu/sites/default/files/publications/publications%20-%20satellite%20-%20special%20report.pdf.
[33] Defense Information Systems Agency, “Information Volume & Velocity (IV2) - DTOMC35011_SS_IV2 (Archived) - Federal Business Opportunities: Opportunities,” accessed April 15, 2015, https://www.fbo.gov/index?s=opportunity&mode=form&id=6fda262f46fab5f5273c18b1607e079d&tab=core&_cview=0.
[34] United Nations Secretary-General, “About | United Nations Global Pulse,” UN Global Pulse, accessed April 15, 2015, http://www.unglobalpulse.org/about-new.
[35] Sheldon Himelfarb, “Can Big Data Stop Wars Before They Happen?,” Foreign Policy, April 25, 2014, http://foreignpolicy.com/2014/04/25/can-big-data-stop-wars-before-they-happen/.
[36] Jan-Frederik Kremer and Benedikt Müller, eds., Cyberspace and International Relations: Theory, Prospects and Challenges, 2014 edition (New York: Springer, 2013), vii.



0 Reacties
Reactie toevoegen